All Credentials
Inside senhasegura are used entities called Devices and Credentials to organized your PAM.
- Devices are elements managed by the solution like Servers, Workstations, Network Assets, Web Apps, and others.
- Credential is the username and password that is associated with a device, which will provide your remote access.
It is important to be aware that every credential belongs to a device. But a credential can be used on multiple devices and products on the platform.
This means that the device must be registered before the credential. But this device does not need to be exactly hardware. It can be a service that is reachable under network address and it may have connectivity within the protocols supported in senhasegura.
The Credentials report is accessed in the PAM Core ➔ Credentials ➔ All menu. This report shows credentials subdivided by the devices to which it belongs.
Only Credentials which the current User has permission to see will be listed on this screen. You can check how Access Groups docs work to manage these permissions.
Actions
Each record has actions to keep or use the credential. Let's explore the credential's special actions.
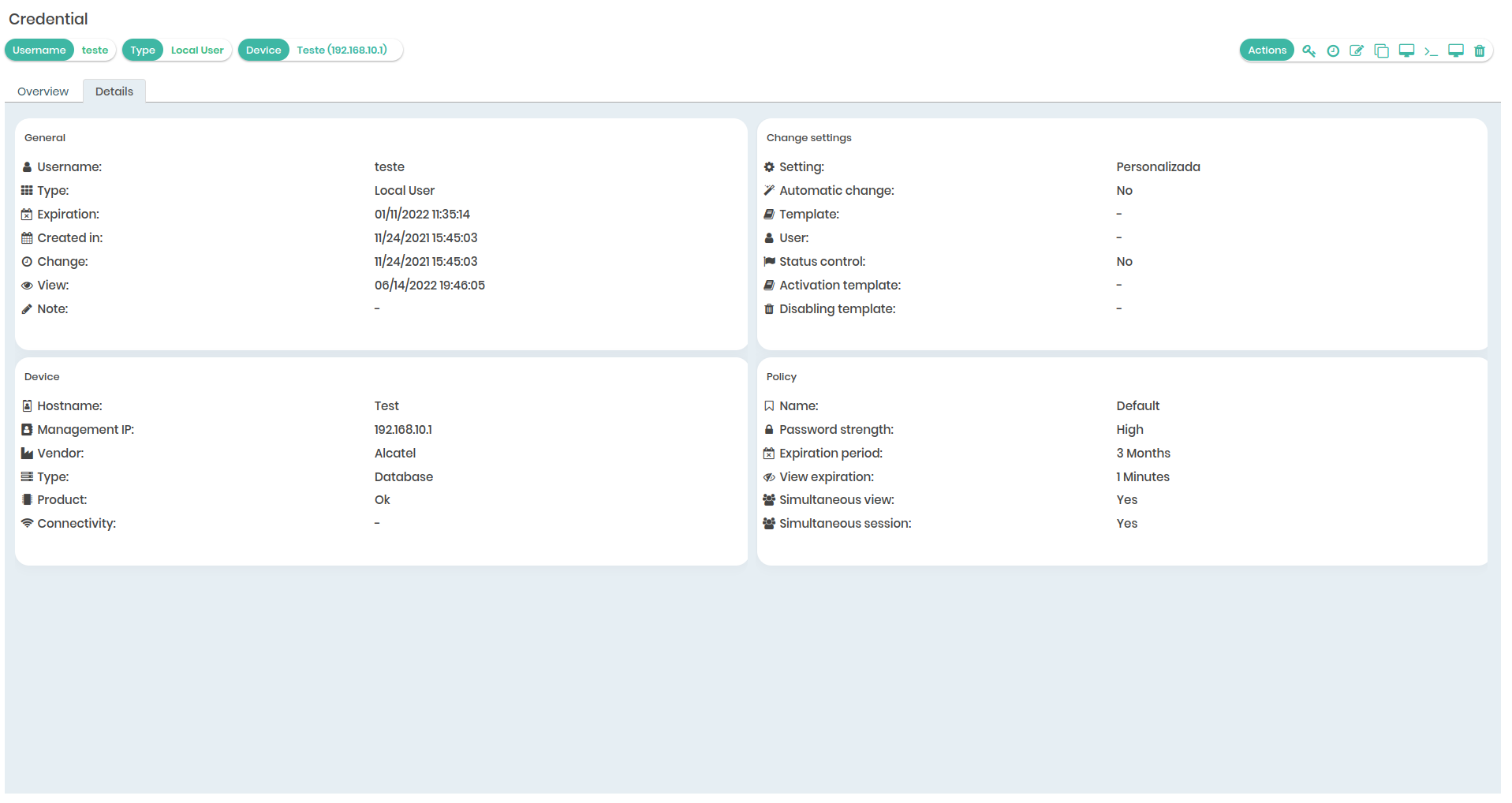
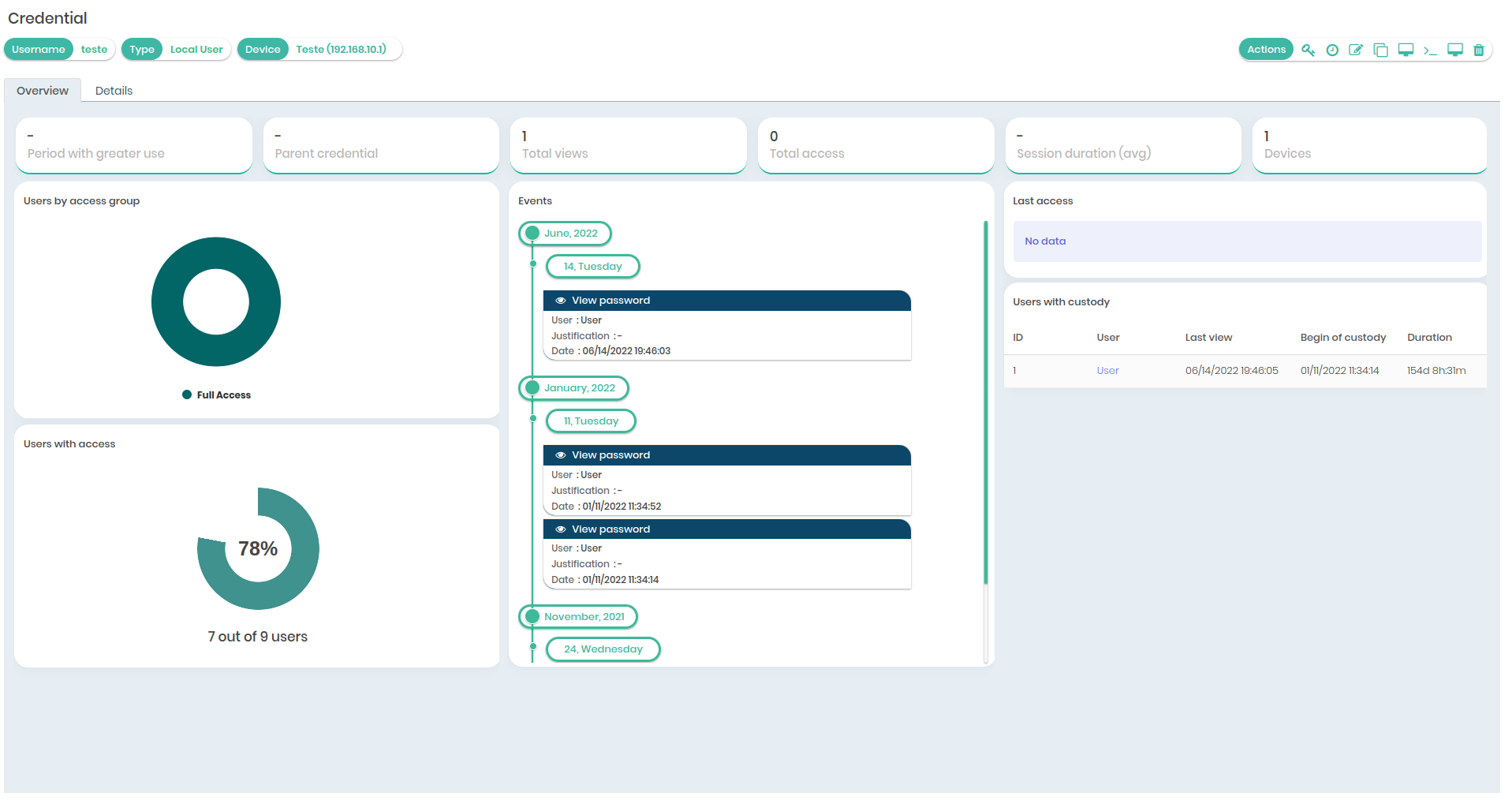
- Details: It brings general information about the credential, timeline of events, accesses, associated devices, password policy in use, and password change settings. In the actions menu, you can access shortcuts for viewing passwords, editing, login, exceptional access, and other options.
History: Get access to the credential password history, and you will be able to access all old values of this password. This action uses the access workflow;
Edit: Allows you to edit information about the credential already registered;
Clone: Allows you to completely clone the credential. Use as a facilitator when you want to create credentials similar in their characteristics. You'll save time by just changing the username and password values;
Exceptional Access: This feature allows you to give access to a specific user on the system and configure their access restriction;
Delete: This feature gives you the option to disable the credential on the system.
View password and Login action can use Access Workflow.
Other Information
Attention: The child credential will always assume the same password as the parent credential.
By inactivating a credential, all users will lost access for that inactivated credential so not being possible use through the proxy (Start Session), Automatic password change, even View Password and history access will be inacesiable.
When you deactivate a device, all credentials linked to the device will be inactivated.
When you activate a device, only the device will be activated. Credentials must be activated one by one manually. This allows the review and assurance that credentials are not improperly activated.