Technical Specification
Introduction
senhasegura is a security platform composed of software, operating system and hardware. This modularized platform meets the most stringent security standards in the industry.
In this document we will cover the main technical aspects of senhasegura .
System Modules Architecture
The senhasegura software solution is divided into the following modules:
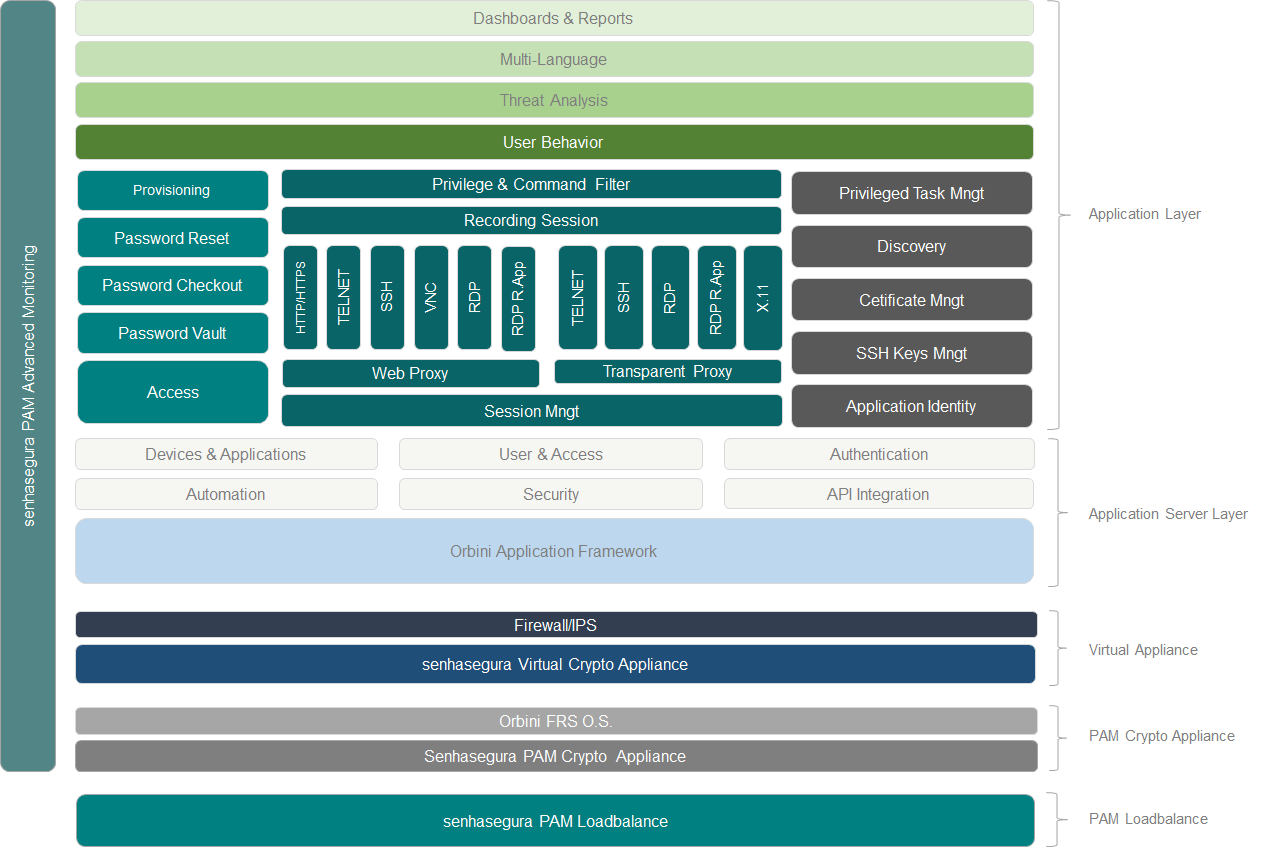
These components support the operation of the senhasegura , from the physical layer to the application layer.
Business layer: where all senhasegura features are located, from integrations to activity recording
Application Server layer: where Orbini is located, MT4 developed framework to support all solution features
Virtual Appliance: virtual device where the solution is executed
Appliance layer: senhasegura hardware solution
Basic Systems Solution Components
In addition to the modules presented, the solution has basic embedded software components integrated into the solution itself, without the need for external resources:
Optimized and hardenized1 over all aspects (Application, Data Base, File System, etc) Linux-based operating system. The system has only the minimum services running, obeying the Minimum Privilege Principle, and kernel adapted to the functionality of the solution.
Own database, no license required
Own and integrated web server
Embedded web interface, no licenses or additional features to use. With just a single network configuration interface, it is already possible for the deployer to have access to the HTTPS web interface so that all other configurations can be performed in a secure and user-friendly graphical environment.
Ports
On virtual and physical appliances senhasegura , only service ports are released:
| Protocol/Port | Function |
|---|---|
| TCP/22 | SSH Server |
| TCP/80 | Web Server with redirection to port 443 |
| TCP/443 | Web Application Server |
| UDP/161 | SNMP |
| UDP/162 | SNMP |
| TCP/3389 | RDP Proxy |
| TCP/3306 | Database cluster |
| TCP/4444 | Database cluster |
| TCP/4567 | Database cluster |
| TCP/4568 | Database cluster |
| UDP/4567 | Database cluster |
Language
The solution has all interfaces in the following languages:
Brazilian Portuguese (PT-BR)
United States English (EN-US)
Germany (DE) [BETA]
Spanish (ES)
Polish (PL) [BETA]
French (FR) [BETA]
Russian (RU) [BETA]
The solution allow user input and storage using UTF-8 charset:
Arabic
Arabic Extended-A
Arabic Extended-B
Arabic Mathematical Alphabetic Symbols
Arabic Presentation Forms-A
Arabic Presentation Forms-B
Arabic Supplement
Basic Latin
Bopomofo Extended
CJK Compatibility
CJK Strokes
CJK Symbols and Punctuation
CJK Unified Ideographs
CJK Unified Ideographs
CJK Unified Ideographs Extension B
CJK Unified Ideographs Extension C
CJK Unified Ideographs Extension D
CJK Unified Ideographs Extension E
CJK Unified Ideographs Extension F
Cyrillic
Cyrillic Supplement
Enclosed CJK Letters a
French
Hangul Compatibility J
Hebrew
Hiragana
Kanbun
Katakana
Katakana Phonetic Exte
Latin Extended-A
Latin-1 Supplement
Syriac
Syriac Supplement
Russian
Yijing Hexagram Symbol
Manuals
The solution has user manuals in the following languages:
Brazilian Portuguese (PT-BR)
United States English (EN-US)
Compatibility ISO 27001, PCI, SOX, GDPR, PQO BM&F
senhasegura enables organizations to deploy the most stringent and complex privileged credential access controls required by standards such as ISO 27001, PCI, SOX, GDPR and PQO by automating privileged access controls, protecting the IT park from data breaches and potential compliance violations.
Component Update
senhasegura Research and Development team is aligned with updates to the third party components that make up the solution. The process of updating these components is done through a fast communication channel, and is performed on customers if a critical demand is released.
The tool update process is aligned with the client's own update policy. In this case, a team will be deployed to fulfill the installation flow with the least risk of impact to the customer's business.
Functional Feature by Modules
The senhasegura do not allow the installation of other softwares.
Base Module - System Access Settings
This module has the following functions:
senhasegura Authentication: senhasegura has its own authentication module with functionality that: Implies in user blocking after a determined amount of unsuccessful login attempts. Change the password in the first login, validation of the complexity of the new password created with comparison of the history of passwords used.
User Registration: Complete user registration with change and configuration traceability.
Profile Management: Advanced granular profile management with ability to create according to each user profile.
Screen's Log: System screen view log.
Screen Identification by codes: Each system screen is uniquely identified with a code, making service and support easy.
External Authentication Servers: In addition to its own authentication module, senhasegura can be used in conjunction with other directory services. You can set up senhasegura to perform authentication across multiple servers, including establishing an authentication order. The main authentication servers that integrate with senhasegura are Active Directory, LDAP, TACACS and RADIUS.
Two Factor Authentication: You can reinforce the authentication process through Multi-factor authentication using, for example, the Google Authenticator application.
IP Access Blocking: senhasegura is able to block access through a pre-established IP denylist.
Session Management: In the tool, the session management module is responsible for checking session validity and setting a timeout until the next login.
Authentication with A1 and A3 Certificates: The authentication process can be carried out using A1 and A3 certificates as the second authentication factor.
Base Module - Password and Information Vault
This module is the core of the password vault, and has the following functions:
Password Guard: Storage of passwords in the vault, encrypted in AES 256 algorithm with double encryption factor. Passwords can only be accessed in this module through the Access Management module.
Protected Information Guard: The password vault allows encrypted storage of information such as tokens, certificates and files in general.
Backup of Secrets: Passwords, protected information, and SSH keys require an independent backup unit in the solution.
The information vault and passwords are responsible for writing the secrets to a backup encrypted by the Shamir algorithm-based master vault key.
HSM Integration: Integration with external or internal Hardware Security Module devices
Base Module - Equipment Register
This module is the password senhasegura interface with the assets that will have their passwords managed, and includes the following functions:
Registration Interface: Where the equipment registration occurs, either by web screen individually, or by the batch registration process.
Connector Management: Each device has ports for connection and protocol for access. This module manages the configured connections and communicates with the devices.
Connectivity Test: Periodically, senhasegura will connect to registered devices and validate their connectivity. Users can be alerted of test results.
Equipment Profile: Equipment types and models have default swap profiles and password templates in the tool. This module relates devices to these policies.
Base Module - Access to Information, Passwords, and Session Policies
The access policy module is the only one with access to the password and information vault, and has the following functions:
Access Workflow: The access workflow initiates an approval process for the delivery of the authenticated session or password. This process has different configurations and routes, depending on the client configurations.
Access Approvation: The access approval function allows the approving user to respond to the access request by:
User screen
E-mail
SMS
Emergency Access
Password Split: This function is responsible for breaking the password in two parts. for segmented delivery, and is relevant for PCI compliance.
Access Control: The access control module unifies the three entities considered in the decision to surrender the credential or access:
Delivery Policy
Involved Users
Related Equipment
The joining of these entities defines the session delivery criteria in the system.
User Timing: The access control module can be synchronized with an authentication server. Users of a particular group on the authentication server are loaded into the senhasegura access groups, making access management easier.
Base Module - Reports
Reporting Configuration: Through the interface, the user can remove or add information to a particular report. You can create a whole new view of information that is useful to your needs.
Shipping Schedule: The reports you create can be set to automatically send to certain users.
PCI Reports: Set of specific reports to meet requirements required by PCI audits.
Audit Trails: senhasegura has reports with all relevant system events. Events can be exported to SIEM and Syslog.
Base Module - Dashboards
System Health: Responsible for graphically displaying the overview of senhasegura hardware and Virtual Machines. You can view data such as I / O, memory, and processing.
Process Monitoring: Monitors execution of key vault processes:
Password Changes
Access Group Synchronisms
Password Reconciliation
Connectivity Tests
Settings Backup
Password's backup
Business Monitoring: Monitors health for credential and information protection:
Number of Passwords changed x Failures
by period
Number of Sessions:
Active and Concurrent x System Average
Recorded (by period)
Average session time logged in
Users logged in to the system
Password Change Module
SSH Password Change: Make the connection and run the default password exchange script on the device using the SSH protocol, without the need for agents installed.
Windows Server: Windows Password Exchange connects to a Windows server and runs local password exchange scripts without the need for agents installed.
Through the use of native Microsoft protocols (RPC, RM / WMI) senhasegura is able to interact with the device using commands from the protocols or through PowerShell commands if protocol support is enabled.
Network Asset: Make the connection and run the default password exchange script on the device using the SSH protocol, without the need for agents installed.
Desktop: Make the connection and execute the default exchange script for that password on that desktop using various desktop-based protocols.
Database: Make the connection and execute the default exchange script for that password in that database using the base protocol.
Password Reconciliation Module
Password reconciliations happen in the same way on servers, network assets, desktops and banks: Access to devices and accounts is periodically performed trying to authenticate with the last password in custody, validating whether custody remains under the password safe.
Windows Session Management Module
Session Delivery: Authenticated session delivery is performed without entering a username or password.
Session Recording: During access to the authenticated session, the system records the session in video and text.
MP4 Video Generation: Recorded video can be generated in mp4 format to be downloaded and uploaded.
Audited Proxy Support: Native audited proxy support for SSH and RDP connectivity of client applications installed on clients. For compatibility between manufacturers, all proxy modules use current encryption algorithms and native protocol.
Management Module - Linux Sessions
Linux Web Session Delivery: Authenticated session delivery is performed without entering a username or password
Web Session Recording: During access to the authenticated session, the system records the session in video and text.
MP4 Video Generation: Recorded video can be generated in mp4 format to be downloaded and uploaded.
Audited Proxy Support: Native audited proxy support for SSH and RDP connectivity of client applications installed on clients. For compatibility between manufacturers, all proxy modules use current encryption algorithms and native protocol.
SSH Gate Session Management Module - senhasegura Terminal Proxy
Linux Session Delivery via SSH Gate: Authenticated session delivery is performed without entering a username or password. This is done transparently to the user through any SSH client.
Web Session Recording: During access to the authenticated session, the system records the session in text.
Command Audit: All commands sent to the server through senhasegura , and can be audited and generated Command Execution alerts.
Privilege Control: It has granular control of commands that can be executed with the possibility of blocking those not authorized for execution to the user.
Audited Proxy Support: Native audited proxy support for SSH and RDP connectivity of client applications installed on clients. For compatibility between manufacturers, all proxy modules use current encryption algorithms and native protocol.
Management Module - HTTP Sessions
HTTP and HTTPS Session Delivery: Authenticated session delivery to a page is done without the need for a username or password.
Web Session Recording: During access to the authenticated session, the system records the video session.
MP4 Video Generation: Recorded video can be generated in mp4 format to be downloaded and uploaded.
Discovery Module
Windows Passwords: Discover administrative credentials on Microsoft platform servers and desktops, identifying which ones are privileged, and importing into the vault.
Linux / Unix / AIX Passwords: Discover administrative credentials on Linux / Unix / Aix servers and desktops, identifying which ones are privileged, and importing into the vault.
AD Passwords: Discover administrative credentials on the Microsoft platform Active Directory server, identifying which ones are privileged, and importing into the vault.
SQL / Oracle Passwords: Discover administrative credentials in databases, identifying which ones are privileged, and importing into the vault.
SSH Keys: Discovers public and private SSH keys that are present on the target device.
Certificates: Find local or Windows user certificates stored in devices, containers or on the domain.
Local Authorities: Find local authorities for the devices.
Services: Find out what services are being performed on the target device.
DevOps: Find DevOps artifacts that are present in the devices.
Glossary of Provisions: Allows to create scan list with segmentation by type
Module A2A - App to App
.Net: Password delivery via lib on .Net to be added to platform application code.
Java: Password delivery via passwords lib in Java to be added to platform application code.
PHP: Password delivery via passwords lib in PHP to be added to the platform application code.
Application Server: Password change in the main Application Servers of the market.
senhasegura API: Password delivery through the senhasegura API.
Module senhasegura.go
senhasegura.go allows you to invoke administrator privileges to run applications on local workstations. This module is based on .NET Framework for 4.8.
Supported Integrations
senhasegura has several types of integration, besides the possibility of configuring integration templates. The templates are open and can be modified by the administrator.
Performing integration may require specific plug-ins. Password architecture and integration features allow senhasegura to develop plug-ins quickly.
senhasegura is noninvasive. Therefore, no agent installation is required on the systems managed by the solution. For some applications it is possible to use senhasegura through agents to create more integration possibilities.
Operational System
| Vendors | Models |
|---|---|
| Apple | OS X |
| Cisco | Cisco IOS, NX-OS (Nexus) |
| EMC | UNIX |
| F5 | Big IP, LTM |
| HP | HPUX, Tru64, NonStop (Tandem), Open VMS, HP5500, Tande |
| IBM | AIX, iSeries, Z/OS, CICS, OS/390 |
| Linux | Fedora, Ubuntu, Red Hat, SUSE Linux, Debian |
| Microsoft | Windows XP, Windows Vista, Windows 7, Windows 8 / 8.1, Windows 10, Windows Server 2003, 2008, 2012, 2016 |
| NetApp | NetApp |
| Oracle | Solaris, Solaris Intel, Enterprise Linux |
| Juniper | JUNOS |
Network Equipment
| Vendors | Models |
|---|---|
| 3Com | Switches |
| A10 Networks | A10 |
| Adtran | NetVanta 838, Tracer 6420 |
| Alcatel | Switches, Switches (Omniswitch 7000 Series), Intelligent Services Access Manager (ISAM) |
| Allot | Allot Secure Service Gateway, Allot Service Gateway, Allot SmartEngage, Allot WebSafe Personal |
| Applied Innovation | AISCOUT-S02 |
| Aruba Networks | ArubaOS |
| Avaya | Media Gateway |
| Avocent | DSView management |
| BlueCoat | PacketShaper |
| Brocade | Silkworm |
| BTI Photonic Systems | NETSTENDER 1030 |
| Cisco | Routers, ACS (Access Control Server), Switches Catalyst, Switches Nexus, JMC, Wireless LAN Controller 5508, WAAS, ONS, ESA (Email Security Appliance), Privilege 15, Unified Communication Manager, ISE (Identity Services Engine), UCS (Unified Computing System) |
| Citrix | Netscaler |
| Dell | Switches |
| Enterasys | Routers, Switches |
| Ericsson | ServiceOn Element Manager (SOME) |
| F5 | BigIP, LTM |
| Fujitsu | FSC iRMC |
| Gemalto | SafeNet KeySecure, SafeNet HSM |
| HP | ProCurve, HPE 5500 |
| Huawei | S1720, S2700, S5700, S6720, S6720 V200R011C10 |
| Juniper | Routers (JUNOS), Pulse secure |
| Mcafee | nDLP |
| Meinberg | Lantime |
| Netscout | Infinistream |
| Nokia | NetAct, DX200 |
| Nortel | BayStack, VPN Router, Ethernet Routing Switch |
| Radware | ISR Infiniband Switch, ODS1 Load Balancer, Alteon, Linkproof |
| Radware | ISR Infiniband Switch, ODS1 Load Balancer, Alteon, Linkproof |
| RFL Electronics | IMUX 2000 |
| Riverbed | CMI, Xilinx |
| RuggedCom | Routers, Switches |
| Symmetricom | Symmetricom Xli |
| Voltaire | ISR Infiniband Switch |
| Extreme Networks | Switch, Router |
| Yamaha | RTX |
Applications Servers
| Vendors | Models |
|---|---|
| Red Hat | Jboss |
| Kaspersky | Kaspersky Endpoint Security for Business |
| Microsoft | SQL Server, Exchange Server 2007 - 2019, entre outras aplicações que permitam interatividade via RemoteApp, Windows RPC e Windows RM |
| Veritas | NetBackup 7.7, 8.0, 8.1 e 8.2 |
| IBM | Websphere Application Server, Websphere Datapower |
| Apache Foundation | Apache HTTP Server, Apache tomcat |
| Oracle | WebLogic Server |
| Microsoft | IIS |
Security Devices (Firewall, UTMs, IPSs)
| Vendors | Models |
|---|---|
| Acme Packet | Net-Net OS-E |
| Aker | Aker Firewall UTM |
| Blue Coat | Proxy SG |
| Checkpoint | FireWall-1, SPLAT, Provider-1, GAIA |
| Cisco Systems | PIX, ASA, IronPort, Mail Gateway |
| Critical Path | Memova Anti-Abuse |
| Fortinet | FortiGate, Fortimanager |
| IBM | DataPower Integration Appliance |
| Juniper | Netscreen |
| Mcafee | NSM (Network Security Manager), SideWinder, ePO |
| Nokia | Checkpoint FireWall -1 on IPSO |
| Palo Alto Networks® | Panorama |
| ProofPoint | Protection Server |
| RSA | Authentication Manager (SecurID) |
| Safenet | Luna HSM |
| Schneider | Industrial Defender |
| SonicWall | Firewalls |
| Sophos | Astaro Security Gateway |
| SourceFire | SourceFire 3D |
| Symantec | Brightmail Gateway |
| TippingPoint | IPS, SMS |
| WatchGuard | Firebox X Edge e-series, Firebox X Core e-series, Firebox X Peak e-series, WatchGuard XTM |
Virtualization Environments
| Vendors | Models |
|---|---|
| VMware | ESX/ESXi Server |
| Citrix | Xen Citrix |
| Microsoft | Hyper-V, Azure |
| Google Cloud Platform (GCP) | |
| Amazon | Amazon Web Services (AWS) |
| Generic | ISO installation media |
Database
| Vendors | Models |
|---|---|
| IBM | DB2, Informix, Datastage |
| InterSystems | Caché Release 2010 - 2017 (and other supported ODBC versions connected to devices with supported connectivity) |
| Microsoft | SQL Server |
| MongoDB | MongoDB |
| MySQL | MySQL |
| ODBC | ODBC compatible databases |
| Oracle | Oracle Database, Oracle Enterprise Manage, RDBMS, Mysql 4 - 8 |
| Postgresql | Postgresql 6 - 11 |
| SAP | HANA |
| Sybase | Sybase Database, IQ |
Storages
| Vendors | Models |
|---|---|
| Dell | Dell EMC PowerMax 2000, Dell EMC PowerMax 8000, Dell EMC SC5020, Dell EMC SC5020F, Dell EMC SC7020, Dell EMC SC7020F, Dell EMC SC9000 , Dell EMC SCv3000, Dell EMC Unity XT 380F, Dell EMC Unity XT 480F, Dell EMC Unity XT 680F, Dell EMC Unity XT 880F, Dell EMC XtremIO X2, Dell PowerVault, Dell EMC VMAX Among other models compatible with supported connections. |
| IBM | Storwize V7000 Gen 3 ”Next Gen”, Storwize V7000 Gen 2+, Storwize V7000 Gen 2, Storwize V7000 family, Storwize V5100E, Storwize V5030E, Storwize V5010E, Storwize V5030, Storwize V5020, Storwize V5010, Storwize V5000 |
| Huawei | OceanStor 18000F V5, OceanStor 5300 V3, OceanStor 5300F, OceanStor 5500 V3, OceanStor 5500F, OceanStor 5600 V3, OceanStor 5600F , OceanStor 5800 V3, OceanStor 5800F V5, OceanStor 6800 V3, OceanStor 6800F V5 Among other models compatible with supported connections |
| NetApp | NetApp ONTAP (BSD) |
Windows applications
| Vendors | Models |
|---|---|
| Microsoft | Applications developed under Java, .Net, PHP, Phyton, SQL accounts, Windows scheduled tasks, Windows services, Apache applications, IIS applications, COM+ services, Clustered applications |
Directory Systems
| Vendors | Models |
|---|---|
| Digi | Digi Remote Manager |
| Fujitsu | iRMC |
| Microsoft | ActiveDirectory |
| Novell | Novell Directory Services (NDS) |
| Sun | Java System Directory Server |
Remote Access and Monitoring
| Vendors | Models |
|---|---|
| Amazon | Amazon Web Services (AWS) |
| Dell | Dell Remote Access Card (DRAC) |
| HP | StorageWorks, iLO |
DevOps environment, VSC and others SDLC softwares
| Vendors | Models |
|---|---|
| Ansible | Ansible |
| Atlassian | Bamboo CI/CD, JIRA Core, Bitbucket |
| GitLab Inc. | GitLab CI/CD |
| Kubernetes | |
| Jenkins | Jenkins CI/CD |
ITSM Tools
| Vendors | Models |
|---|---|
| Atlassian | Jira Service Desk |
| Zendesk | Zendesk |
| Freshworks | Freshdesk |
| ServiceNow | ServiceNow ITSM |
TOTP Tools
senhasegura 2FA function works with any Time-based One-Time Password (TOTP) tool. Here you can see some options:
| Vendors | Models |
|---|---|
| Google Authenticator | |
| Microsoft | Microsoft Authenticator |
| Authy | Twilio Authy 2-Factor Authentication |
| Red Hat | FreeOTP Authenticator |
| Sophos | Sophos Authenticator |
| LastPass | LastPass Authenticator |
| andOTP | andOTP |
Integration Plugins
| Integration | Function |
|---|---|
| Jenkins | Allows the consultation of secrets in the senhasegura |
SIEM Solutions
| Vendor | Model |
|---|---|
| Exabeam | Version i31 onwards. |
| IBM QRadar | Version 7.3 onwards. |
| LogRhythm | Version 7.4 onwards. |
| Rapid7 - InsightIDR | Version 20180814 onwards. |
| Rapid7 - InsightOps | Version 20190204 onwards. |
| Securonix | Version 6.3 onwards. |
| Splunk | Version 6.3 onwards. |
SSO solutions
| Vendor | Model |
|---|---|
| Okta | Lifecycle Management |
| RSA | RSA SecurID |
| Duo | Duo Multi-factor Authentication |
Embedded browser version
| Tool | Version |
|---|---|
| Firefox | 78.13.0esr (64-bit) |
Encryption and Security Features
Encryption
All sensitive information provided is stored encrypted in the solution database using the AES-256 cipher.
For authentication to the senhasegura web interface - both locally and via external authentication servers - all user passwords are stored in SHA-256 hash format. The communication between the client workstation and the senhasegura is made through encrypted communication respecting the encryption standards of the protocols used. Independent of the communication channel, be it RDP, SSH or HTTPS.
Likewise, access to remote target devices respects the same encryption standard in all protocols that allow configuration.
HSM Encryption
For companies that need a higher level of security, you can opt for the Hardware Secure Module (HSM), a hardware security and encryption device with military specification and tamper-evident standards.
HSM Technical Specifications
Encryption
RSA (PKCS #1 V2.1) (1024, 2048, 4096 bits)
ECDSA (NIST FIPS PUB 186-3)
FIPS 197 AES 128, 192, 256
FIPS 46-3 DES/3DES
Supports certificates x509v3
Supports import and internal key generation
Random Number Generator
Internal, hardware based
Meets AIS31 P2 standard
Real time clock (RTC)
Internal, maximum deviation of 1 minute per year
Appliance and Appliance Security Features
HSM Kryptus
HSM Thales
HSM GEMALTO
HSM DINAMO
HSM YUBICO
Encryption for SSH sessions
Symmetric ciphers
3DES
AES128-cbc
AES192-cbc
AES256-cbc
rijndael-cbc
AES128-ctr
AES192-ctr
AES256-ctr
AES128-gmc
AES256-gmc
chacha20-poly1305
Symmetric ciphers that support authenticated encryption
AES128-gmc
AES256-gmc
chacha20-poly1305
MAC
hmac-sha1
hmac-sha1-96
hmac-sha1-256
hmac-sha1-512
hmac-md5
hmac-md5-96
umac-64
umac-128
hmac-sha1-96-etm
hmac-sha1-256-etm
hmac-sha1-512-etm
hmac-md5-etm
hma-md5-96-etm
umac-64-etm
umac-128-etm
Key exchange algorithms
diffie-hellman-group1-sha1
diffie-hellman-group14-sha1
diffie-hellman-group14-sha256
diffie-hellman-group16-sha512
diffie-hellman-group18-sha512
diffie-hellman-group-exchange-sha1
diffie-hellman-group-exchange-sha256
ecdh-sha2-nistp256
ecdh-sha2-nistp384
ecdh-sha2-nistp521
curve25519-sha256
Certificate Key
ssh-ed25519-cert-v01
ssh-rsa-cert-v01
ssh-dss-cert-v01
ecdsa-sha2-nestp256-cert-v01
ecdsa-sha2-nestp384-cert-v01
ecdsa-sha2-nestp521-cert-v01
Key types
ssh-ed25519
ssh-ed25519-cert-v01
ssh-rsa
ssh-dss
ecdsa-sha2-nestp256
ecdsa-sha2-nestp384
ecdsa-sha2-nestp521
ssh-rsa-cert-v01
ssh-dss-cert-v01
ecdsa-sha2-nestp256-cert-v01
ecdsa-sha2-nestp384-cert-v01
ecdsa-sha2-nestp521-cert-v01
Availability and Contingency
The senhasegura system supports operation on virtual or physical appliances. The senhasegura virtual appliance is customized for installation without releasing administrative users in the operating system.
In any configuration, the system supports high availability and external contingency disaster configurations.
High Availability
Contingency and Disaster Recovery
Backup
senhasegura has several mechanisms to recover information in case of failure:
Encrypted Password Backup
External in client infrastructure. The backup file of this information is password protected, which is distributed in multiple custody among trusted participants at the client's free choice. At least two custodian users are required to receive and retrieve the information. Once the senhasegura delivery ceremony has taken place, all passwords to the safe will be reset and the client will receive their respective custody, except for the passwords to the senhasegura database and operating system.
From version 3.10 on the backup procedure will also be performed for user passwords and Access Keys of the DevSecOps module.
Backup Fast Recovery
Internal and rapid recovery. Stores more critical information, is considered faster, because with the content of the base available the environment is recovered quickly and already becomes accessible upon request.
Encrypted Backup of Settings
Allows not only the stored data but also the password settings to be available for retrieval. This backup is not enabled by default, but its activation is available in system settings.
Safe Video Backup
The senhasegura allows the backup of the videos to be stored in a remote directory under the responsibility of the client. By default the videos are stored in the solution's file system.
Secrets Backup
The backup of secrets: console credentials and access keys are stored in dedicated directories.
Monitoring and Syslog and SIEM
senhasegura has monitoring capabilities designed to alert administrators of any process, integration, connectivity, or access failure.
This system issues on-screen alerts to the administrator or via email, SMS, snmpmibs and snmptraps.
The solution can be integrated with any industry tool using SNMP V1, V2 or V32 standard.
Integration with Syslog and SIEM services.
Own integration with ArcSight.
Browser Compatibility
The senhasegura web interface is accessible only through HTTPS protocol, and it is recommended that you provide your own SSL certificate in accordance with current security assumptions.
senhasegura uses HTML5 and WebSocket technology and only browsers that support these technologies will provide a complete passwords security experience. It also maintains compatibility with browsers in their most recent versions:
Internet Explorer
Google Chrome
Microsoft Edge
Mozilla Firefox
Network Operating Conditions
Connections between users and the senhasegura application have a minimum bandwidth of 180 Kbps per remote session without loss of functionality.
Connections between users and the senhasegura application have a maximum latency of 900 ms without any loss of functionality.
senhasegura application allows IPV4 and IPV6 protocol support following IETF RFC 2460 specification.
Supported Protocols and Ports
senhasegura allows the use of several protocols, through their respective standard ports or any other configured in the solution, for the following operations: remote connections, password changes, Scan Discovery, authentication and web access.
Operations are performed based on the ports configured on the device.
| Connectivity | Default Port | Description |
|---|---|---|
| HTTP | 80 | Web Access |
| HTTPS | 443 | Secure Web Access |
| LDAP | 389 | Scan Discovery / Authentication |
| LDAPS | 636 | Password Change / Scan / Discovery / Authentication |
| MySQL | 3306 | Remote Connection* / Password Change |
| Oracle | 1521 | Remote Connection* / Password Change |
| PostgreeSQL | 5432 | Remote Connection* / Password Change |
| RDP* | 3389 | Remote Connection |
| RM HTTP | 5985 | Password Change / Scan Discovery |
| RM HTTPS | 5986 | Password Change / Scan Discovery |
| SQL Server | 1433 | Remote Connection* / Password Change |
| SSH | 22 | Remote Connection / Password Change |
| Telnet | 23 | Remote Connection / Password Change |
| VNC** | 5900 | Remote Connection |
| Windows RM | 5986 | Password Change |
| Windows RPC | 135 | Password Change / Scan Discovery |
| X11 Forward** | 22 | Remote Connection / Password Change |
The supported protocols are only available on TLS1.2 and TLS1.3, once connected to the senhasegura vault.
*RemoteApp only
**graphical interfaces
Performance
The senhasegura architecture is designed for maximum performance in all operations performed through the solution.
All tests were performed on senhasegura PAM Crypto Appliances with the following configuration:
Hardware Settings
Model: senhasegura PAM Crypto Appliance Titanium
Processor: Intel E5-2630v4
RAM Memory: 128GB
HD: 2x2TB NLSAS RAID1
senhasegura Settings
Cores: 38 vCPUs
RAM Memory: 126GB
HD: 2TB
SSH sessions via senhasegura Terminal Proxy
| Connections | CPU | RAM | DISK W |
|---|---|---|---|
| 500 | 5% | 10GB | 4.500 KB/s |
| 2000 | 20% | 50GB | 6.000 KB/s |
| 3500 | 55% | 85GB | 8.000 KB/s |
SSH sessions via senhasegura Web Proxy
| Connections | CPU | RAM | DISK W |
|---|---|---|---|
| 250 | 10% | 10GB | 7.500 KB/s |
| 750 | 35% | 15GB | 5.000 KB/s |
| 1250 | 45% | 20GB | 2.000 KB/s |
RDP sessions via senhasegura RDP Proxy
| Connections | CPU | RAM | DISK W |
|---|---|---|---|
| 500 | 5% | 15GB | 8.500 KB/s |
| 1250 | 10% | 30GB | 5.000 KB/s |
| 2000 | 15% | 50GB | 2.000 KB/s |
RDP sessions via senhasegura Web Proxy
| Connections | CPU | RAM | DISK W |
|---|---|---|---|
| 250 | 5% | 10GB | 16.000 KB/s |
| 1000 | 10% | 20GB | 9.000 KB/s |
| 1750 | 20% | 30GB | 1.000 KB/s |
Web HTTP Connections (High Usage)
| Connections | CPU | RAM | DISK W |
|---|---|---|---|
| 10 | 10% | 5GB | 2.100 KB/s |
| 20 | 18% | 10GB | 1.800 KB/s |
| 30 | 20% | 15GB | 1.500 KB/s |
Web HTTP Connections (Medium Usage)
| Connections | CPU | RAM | DISK W |
|---|---|---|---|
| 10 | 10% | 4GB | 80.000 KB/s |
| 20 | 20% | 8GB | 40.000 KB/s |
| 30 | 20% | 10GB | 10.000 KB/s |
Connections Web HTTP (Low Usage)
| Connections | CPU | RAM | DISK W |
|---|---|---|---|
| 10 | 10% | 10GB | 40.000 KB/s |
| 35 | 20% | 15GB | 20.000 KB/s |
| 60 | 30% | 20GB | 10.000 KB/s |
Resource limit
The platform senhasegura has some features that are technically limited, either for reasons for database limitations, operating system limitations, file-system limitations or software architecture limitations.
The limitations relating to contract or license are fixed by contract, and will not be addressed in this topic.
The limitations relating to the number of contracted instances, in a cluster scenario, will also not be addressed in this topic. We will focus on limitations on an instance and its components.
User Limit
Technically, the application will support up to 16,500,000 user records. This number is shared with WebService A2A users, service users, and actual system users. This number does not express the ability of all these users are using the system simultaneously. Simultaneous use capacity may vary according to the type of use, quantity of contracted instances and network latency supplied.
Device Limit
The technically application will support up to 16,500,000 device records. This number contains even inactivated devices over time. This number does not express the ability of all these devices are being accessed via proxy, or any other asynchronous process that accesses the device simultaneously. The ability to manage devices can vary by the number of contracted instances, supported systems and protocols and the network latency provided.
Credentials Limit and Protected Information
The application technically will support up to 16,500,000 credential records. This number contains even inactive credentials over time. This number does not express the ability of all these credentials are being accessed and used by asynchronous tasks or proxy sessions simultaneously. The ability to manage credentials can vary by the amount of contracted instances and the network latency provided.
Proxy session recording
Different from other market solutions, the senhasegura does not perform screen captures in image format, or real-time mp4 videos or other media formats. The real persistence of protocol ensures a faithful and optimized copy of the session. Inactivity times are recorded through 4Bytes timestamp per second, unlike screens capture that would consume much more resources. Native format recording of the protocol already considers the native compression format of the protocol.
User behavior will define the amount of sessions that can be stored. Not excluding the possibility of disk expansion or remote storage mapping to increase storage capacity.
This combination of factors makes the limit of sessions virtually unlimited. Consider the performance table described in the techspec-performance session to calculate your need.
Simultaneous proxy sessions
The amount of simultaneous sessions may vary with the amount of contracted instances, making the solution appropriate to its need without excessive hiring of resources. The cluster architecture also allows the definition of dedicated nodes for specific protocols, or the definition of dedicated instances for different datacenters or network segments. This combination of factors makes the limit of sessions virtually unlimited. Consider the performance table described in the techspec-performance session to calculate your need.
senhasegura versioning
The senhasegura versioning nomenclature follows the M.N.P format (eg: 3.22.1-9):
| Release Type | Description |
|---|---|
| M - Major | Includes profound architecture and/or technology changes. |
| N - Minor | Includes new features and/or improvements to existing features. Also includes known bug fixes and minor architectural changes. |
| P - Patch | Includes critical bug fixes and security patches. (immediate update recommended) |
New versions frequency of release
senhasegura N Updates can vary from 1 to 5 months, depending on the period of the year.
As for the available formats, there are two ways:
- For the new senhasegura environment, can be used the virtual machines available in the partner support.
- Updates are always available through our repositories, with new releases updated as soon as they become available.